The Attendees are now in the tenant and being added automatically based on registration. Before we designed our team experience we needed to ensure that the tenant was configured so that everyone was secure and had the Teams experience we wanted out of the box.
First, we knew we would need a dedicated tenant for the conference. No sharing our personal tenants, not only because of tenant name, but more so to ensure that we had a consistent production ring tenant that had a stable code base to work from. Working with latest features is great for technical development. But for something as big as a conference, you don’t want to be running an early ring release of anything.
Securing Guest Access
One of the first tasks for us was to ensure that no one but ourselves as Organisers could invite Guests to the tenant. This was important because it prevented Attendees, Sponsors and Attendees from inviting people that we weren’t prepared for.
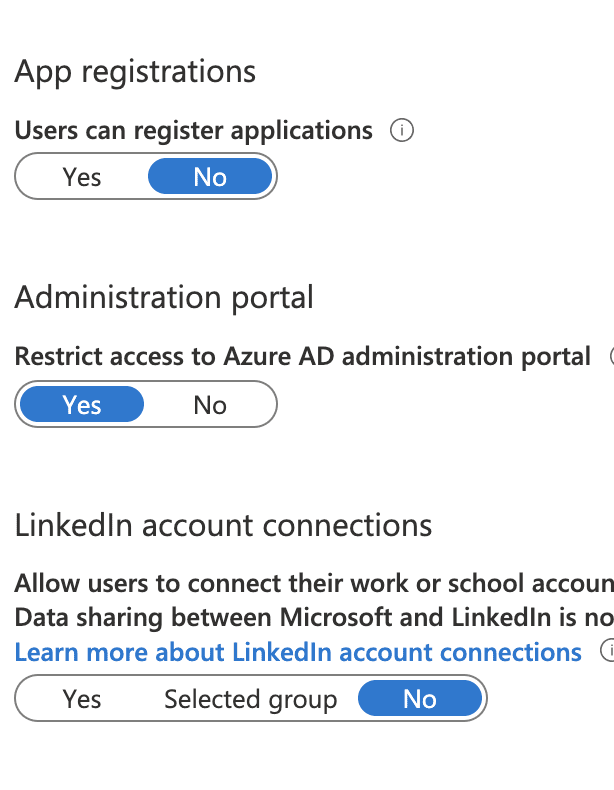
To do this we modified the User settings of AzureAD on the tenant. We disabled the ability to register applications, restricted access to the AzureAD admin portal and turned off the ability for people to connect their LinkedIn Accounts.
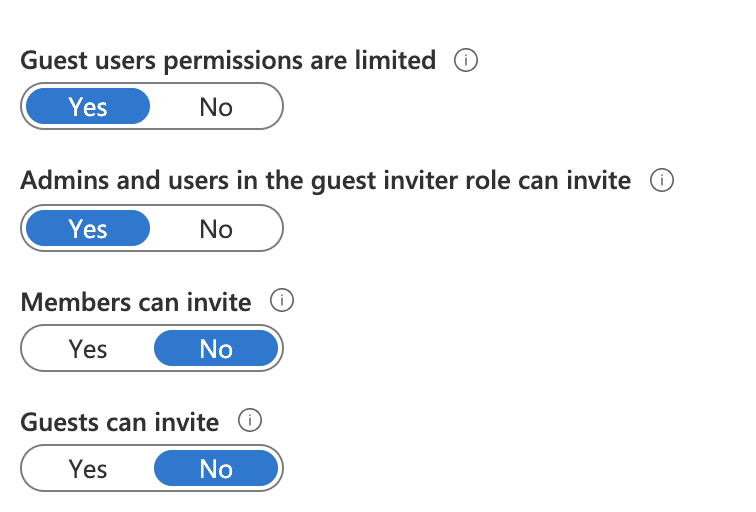
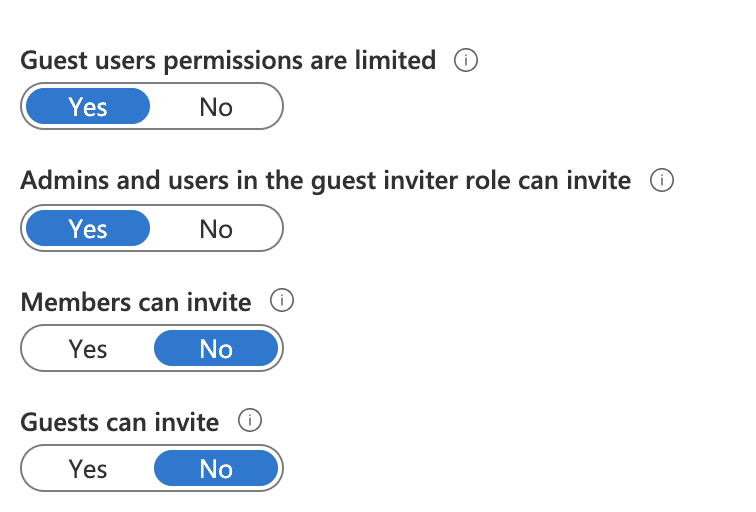
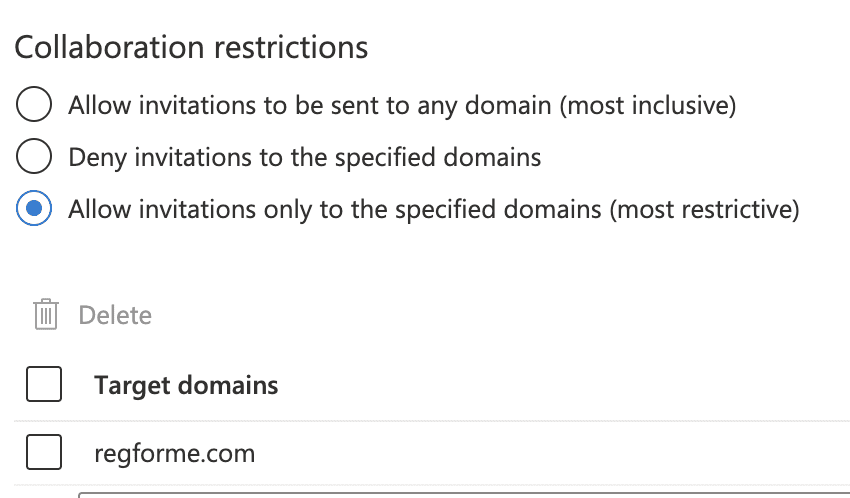
Next, we modified the External collaboration settings for AzureAD. We disabled Members can invite, Guests can invite others and limited guest user permissions.
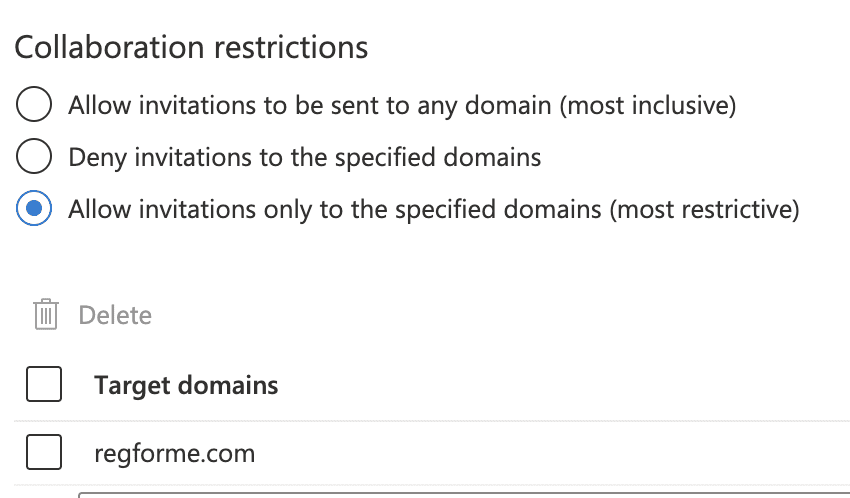
Lastly, we restricted the invitations so that they could only be sent to our auth tenant.
Securing Microsoft Teams
We wanted everyone to experience Microsoft Teams in all it’s glory. However, we wanted to take some measures to ensure that people couldn’t dilute or otherwise complicate the team by adding random apps and tabs etc.
Step 1 – Disabling Third Party Apps
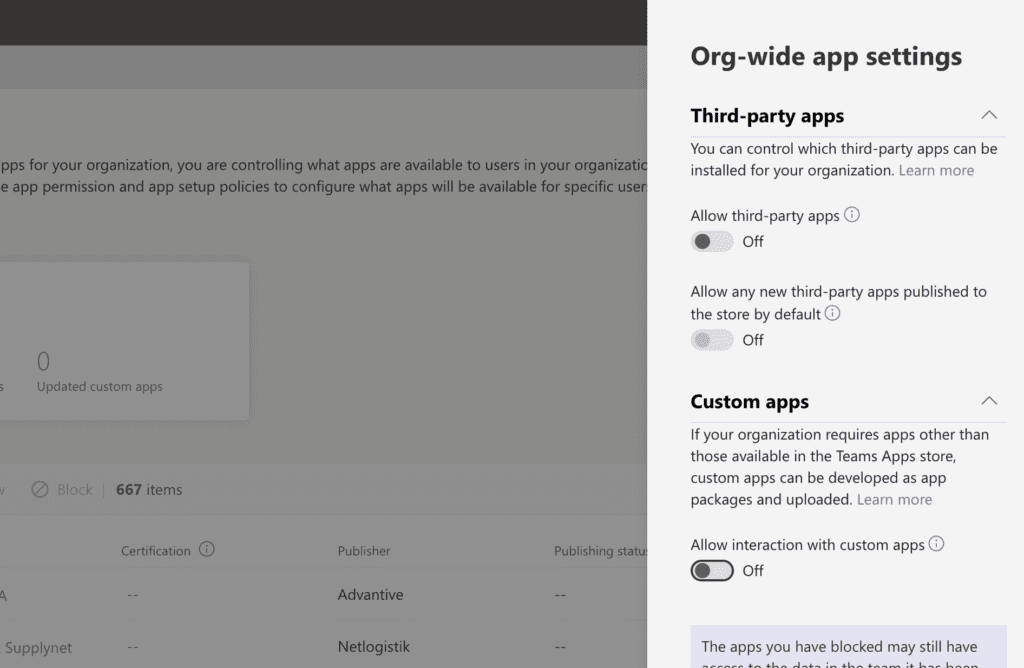
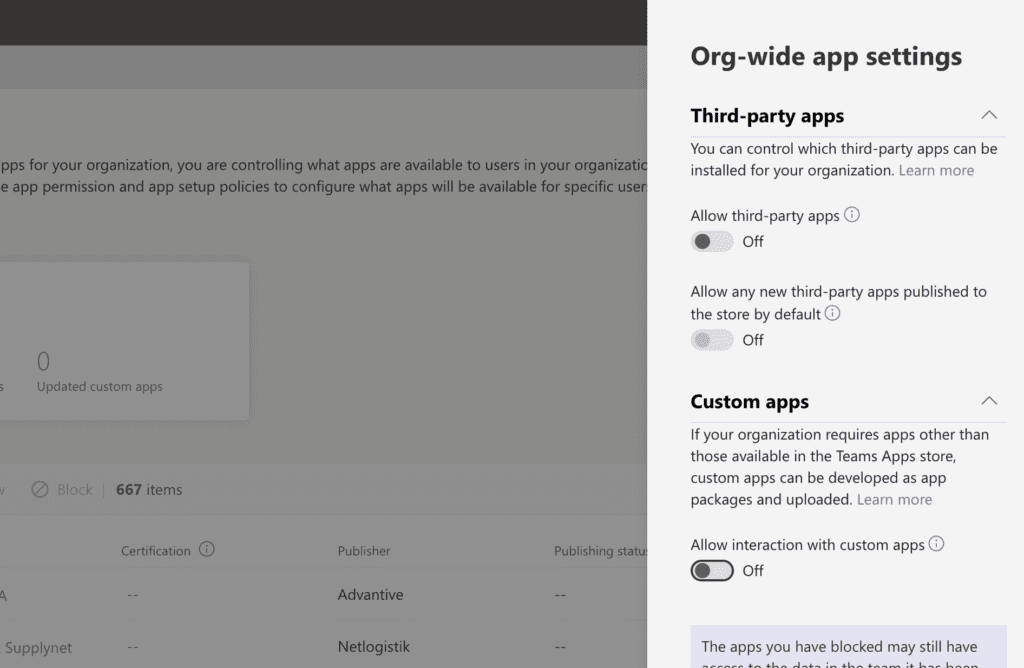
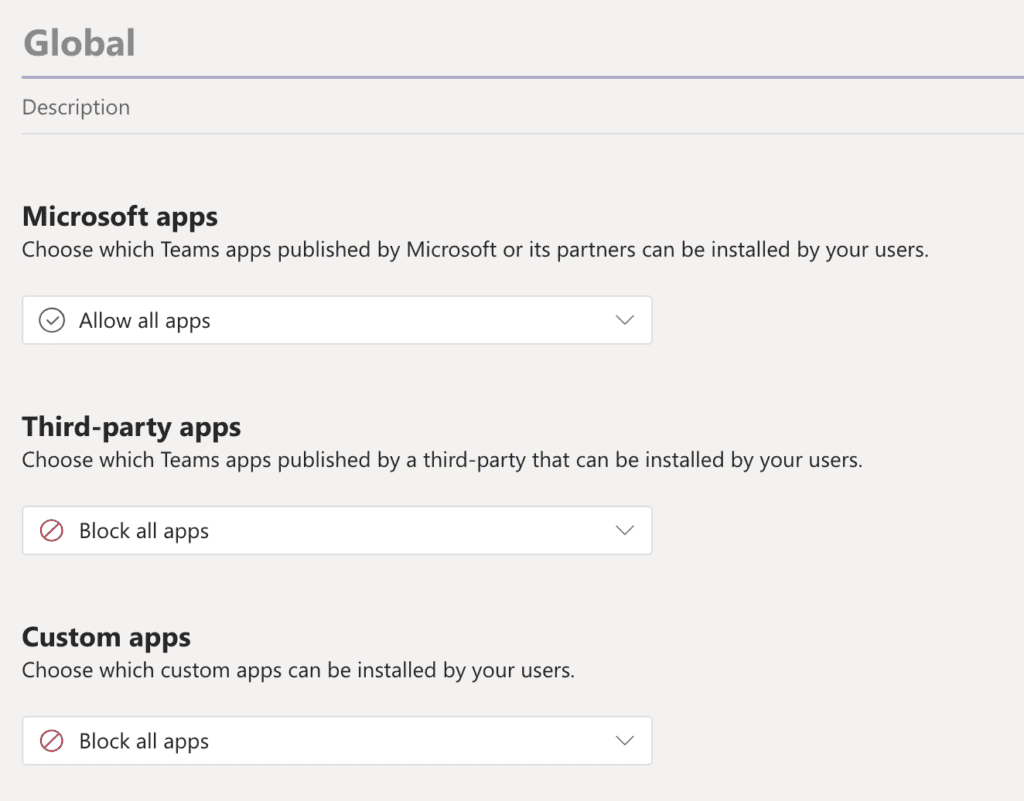
First to disable adding of 3rd party apps. We didn’t want apps in the team that weren’t going to be used. In the Teams Admin Center (TAC) under Teams Apps / Manage Apps and Org wide settings, we turned them off.
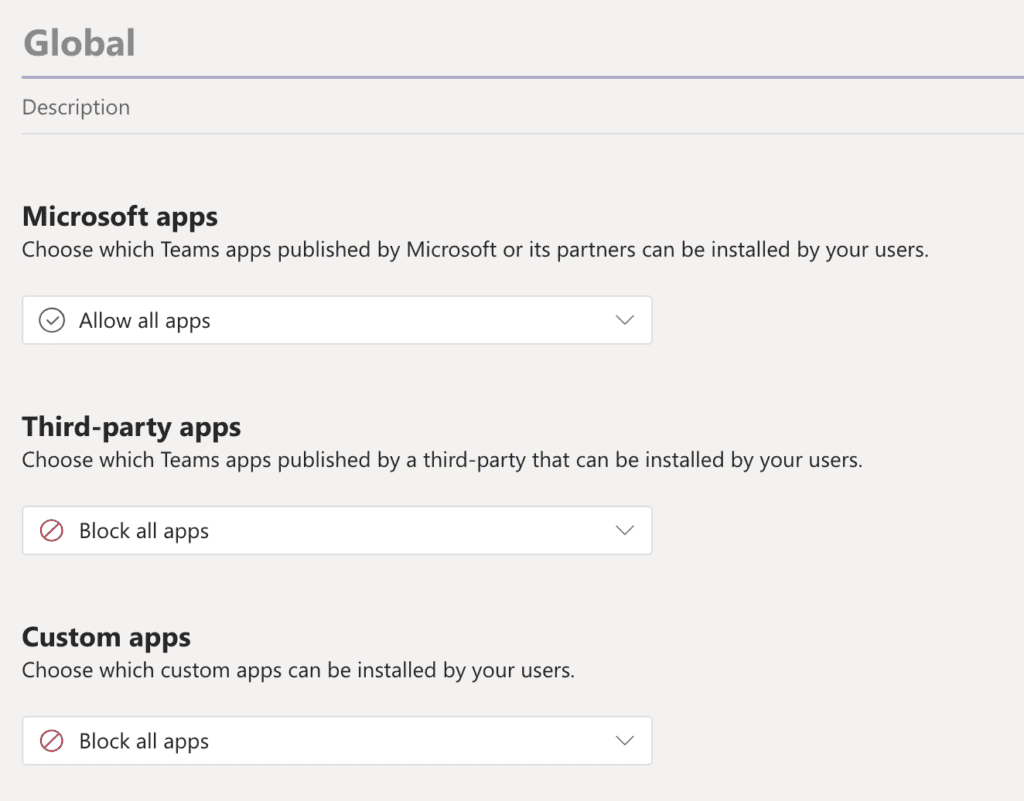
Next for added measure we prevented any apps other than Microsoft ones being installed by any user using the Global permissions policy under the same menu, but Permissions Policy
Step 2 – Setting the Guest Access Experience
Guest Access permissions and experience is managed under Org Wide Settings in the TAC. The normal meeting and calling user policies do not apply in this case. Every guest receives the same standard experience.
For our conference we didn’t want to restrict what Guests (Attendees) could do, so we left these settings to enabled.
Step 3 – Teams Settings
In Teams Settings under Org Wide Settings menu in the TAC, you can enable / disable some file and organisational settings. Our Sponsor staff where licensed members and we had to ensure that they couldn’t connect services or see beyond the team they were in.
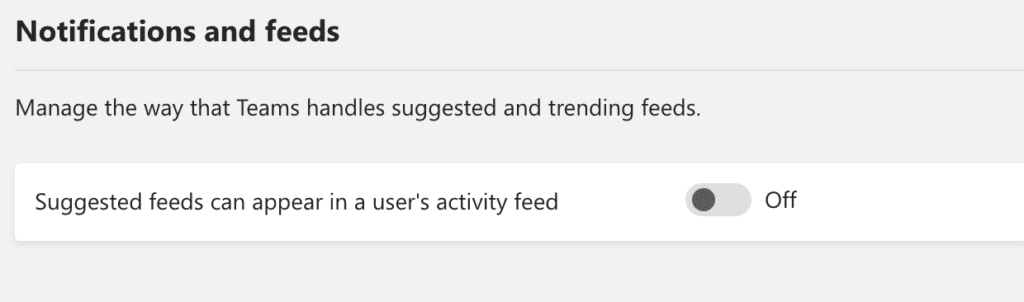
First setting to turn off, notifications and feeds and disabling suggested feeds. It removes unwanted clutter.
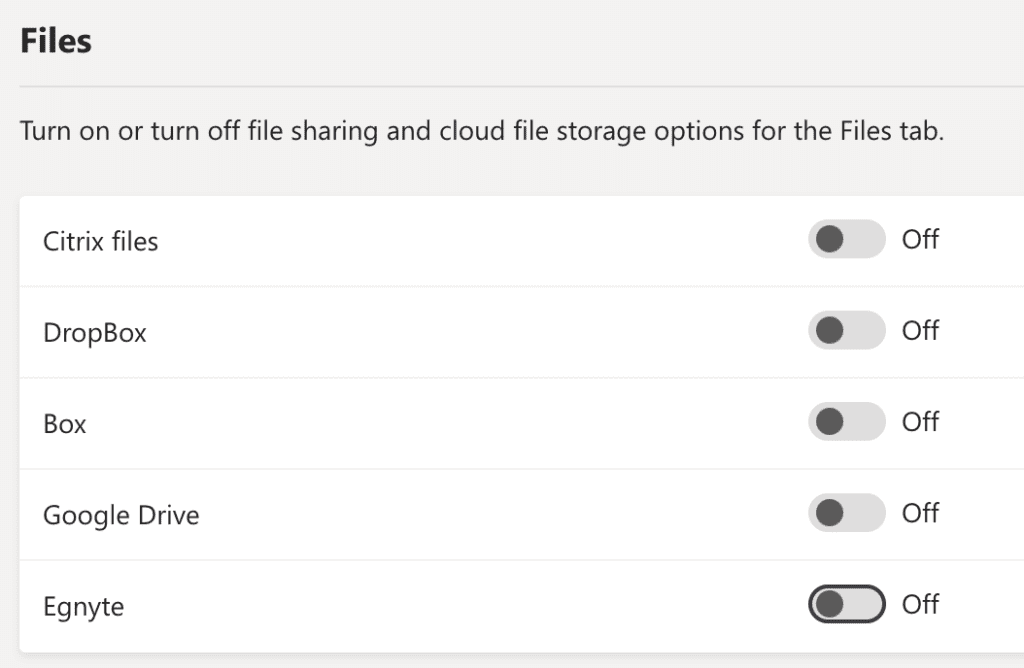
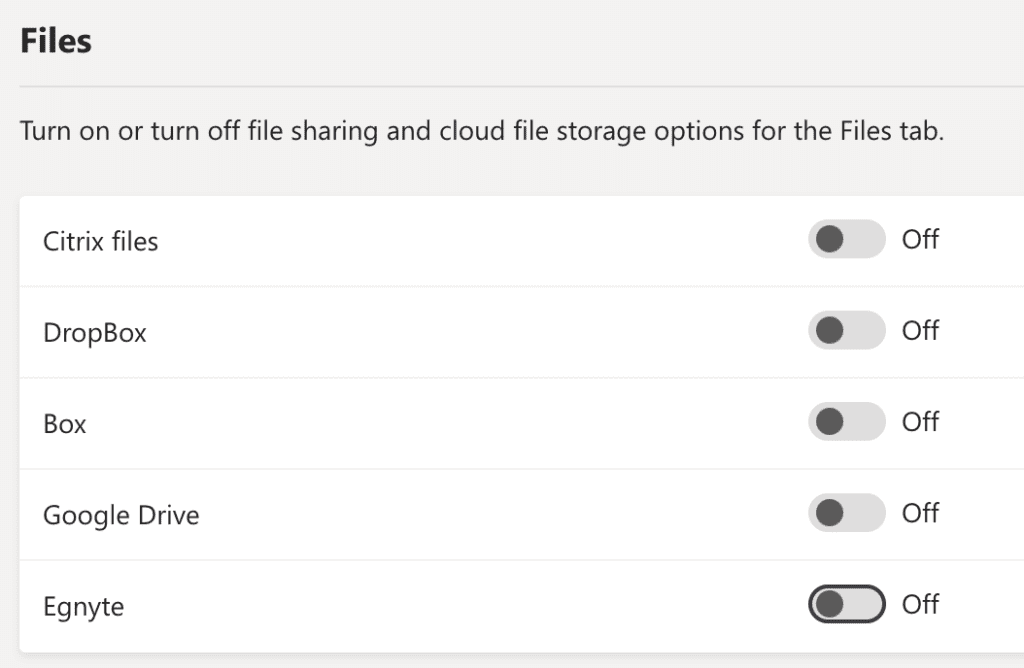
Next, we didn’t want any outside cloud storage. This was a protection mechanism for licensed users (Sponsors). We didn’t want them to accidentally breach their own corporate policies and potentially connect an archive with sensitive data. Neither did we want the admin headache of supporting them with the “How do I do?” e-mails.
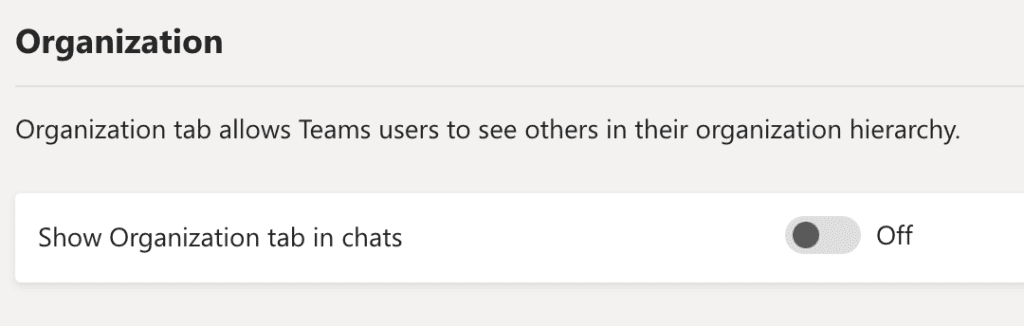
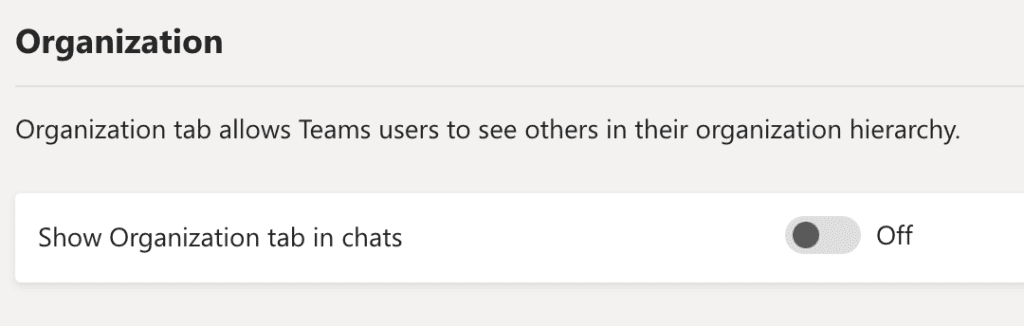
Lastly, not that we had an organisation chart, but we didn’t want that there in the team because by being there opens up room for a question as to why it isn’t working.
Setting The Default Meeting Experience
Our conference was going to be a mix of Teams Live Events and Teams Meetings to deliver the interactive visual and verbal experience to Commsverse.
Our sessions where going to be Teams Live Events for all presentation style and Teams meetings for panel and breakout meetings. More on the use case of these in Part 6.
We knew that in all cases a Live Event or Meeting was going to take place without the organiser, or account that created the meeting and instead be produced or chaired by someone else and most probably a Guest. Therefore, it was paramount that we removed the entry barriers.
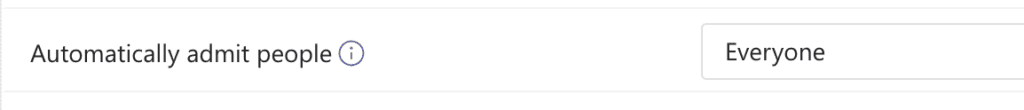
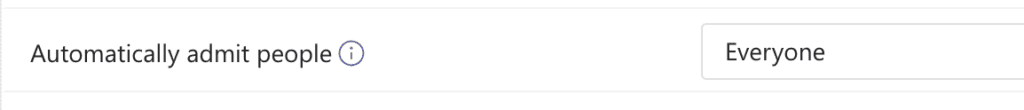
We set the Global Teams meeting policy to bypass the lobby so that anyone could join the meeting without waiting for someone to admit them.
Teams Live Event Policy
We changed the Teams Live Event Global policy to only permit people within the organisation entry. This effectively made it impossible by accident to create public Teams Live Events and we enabled them to be automatically recorded.
That was it as far as AzureAD and the backend of Teams was concerned.
Part 5 – Building the Team
